Tag: Cyber Security
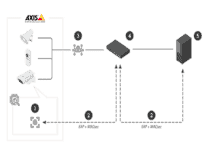
Axis OS 11 Products Support IEEE 802.1AE MACsec
The IEEE 802.1AE MACsec security standard is supported by the AXIS OS 11.8 system for more than 200 network devices.
Manufacturers: Ready For Industry 4.0 Cybersecurity Implications?
Recent breaches of MGM and Caesars are proof that no company — or industry — is safe from sophisticated, aggressive and frequent cyber attacks.
How Disinformation Could Derail OT Security Risk Management
Security teams need to prepare for the potential for disinformation to impact operational technology (OT) security.
How To Prevent The Three Most Common Cyber Threats To Building Systems
Botnets, cryptojacking, and backdoors create major cybersecurity risks for FMs.
Returning To The Office? 10 Tips To Minimize Data Security Risks
New survey finds 77 percent of business managers believe their organizations are likely to experience a data breach in the next three years.
Six Ways To Modernize Your Building Management System
These six building management goals will help create a simple path to creating sustainable, efficient, and cyber secure facility operations.
Modernizing Your Building Management System
Discover a simple path to creating sustainable, efficient, and cyber secure building operations for today and tomorrow.
Is Your Critical IT Infrastructure Ready For Hurricane Season?
Facility executives should consider these strategies to keep critical IT infrastructure up and running through the unpredictability of hurricane season.
Tenable Enhances ServiceNow Cyber Security Partnership
ServiceNow’s The Now Platform now boasts asset inventory and vulnerability data from Tenable.ot, streamlining and centralizing IT and OT vulnerability data.
Tech-driven Innovations Shaping The Metaverse Into Reality
GlobalData, a leading data and analytics company, highlights several use cases that display the potential of the metaverse for business and industry.
Next Steps In Cyber Secure Lighting
As connected lighting gains ground, “turning on the lights” increasingly means tapping into a network of advanced control technology. It also presents cybersecurity concerns.
Securing A Networked Lighting System
When planning a smart lighting system, here are tips to maximize the benefits and address potential cyber security threats.
Netwrix Auditor X Detects Sensitive Data Threats
The new functionality in Netwrix Auditor X enables customers to reduce the time to detect and investigate incidents involving sensitive data.
KMC Controls, Veridify Security Partner To Make Buildings Cyber Safe
DOME provides a low-cost, easy-to-implement security platform that delivers real-time authentication and data protection to the edge of a building’s network.
Cyber Security For Building Networks
As the threat grows, facility management has an expanded role protecting operational technology.
Essential Security Trends For FMs
From common risks to emerging threats, solutions for facilities teams are evolving and maturing.
Wattstopper Digital Lighting Management Products Certified Cybersecure
Legrand announces its Wattstopper Digital Lighting Management (DLM) product family of networked lighting control systems is certified through the ioXt Alliance Certification Program.
Cybersecurity Concerns Continue For Building Systems
Building automation systems are a pathway for hackers to gain wreak havoc on organizations, including their facilities.
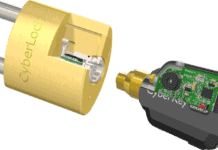
CyberLock Launches Generation 2 CyberLock Cylinders
This latest advancement in key-centric access control offers AES-256 encryption between lock and key.
Cybersecurity For Facilities Calls For Team Effort
To protect facilities, physical security and cybersecurity are increasingly intertwined.


































![[VIDEO] Collect Asset Data at the Speed of Walking a Building](https://facilityexecutive.com/wp-content/uploads/2024/02/maxresdefault-324x160.jpg)